by admin | Apr 11, 2015 | Tech Talk
Auza.Net started its Summer OJT Program for the year on April 6, 2015 with ten students qualifying for the annual training program. All of the trainees that qualified were from the different campuses of the Bohol Island State University taking computer related courses.
This year, the trainees will implement mobile friendly versions of various websites owned or operated by Auza.Net. The current trend in use of mobile devices pose a challenge to web developers because they need to deal with varying screen sizes and hardware.
They will also implement an enterprise ready financial system for a clinic in Talibon and a resort in Dauis. This years batch of trainees will also implement a mobile app on both Android and iOS platform.
In addition, the trainees, who will graduate next school year, will be introduced to the concepts of entrepreneurship as well as learn about personal finance to help them ensure their success after graduation.
On its first weekly progress meeting held on April 11, Jerome Auza, Technology Consultant of Auza.Net, emphasized to the trainees that they should utilize their time and the resources allocated by the company to not only learn about technical matters but also on how to become professionals.

The Auza.Net On-the-job trainees for Summer 2015 with Jerome Auza, Technology Consultant of Auza.net (Top row, left) and the trainees: L-R, top row: Mark Lourenze Opalla, Glenn Kudemus, Mabelle Ruiz, Jaidie Lou S. Santillana, Cristy Malmis, Jhunie Ray Suarez; L-R bottom row: John Cedrick Janohan, James Bayocot, Jaymar Añasco, Stephen Felicio Dalis.
by admin | Mar 28, 2015 | Tech Talk
by: Jerome Auza
In my career as an IT professional, I have learned a lot technically from the works of Richard Stallman, the founder of the Free Software Foundation. So obviously, when I heard he was giving a talk to students and IT enthusiasts at the University of the Philippines – Cebu City, I took this rare chance to meet the man who influenced the direction I took as a software developer.
As he spoke, I can really sense his passion on ensuring that the current and future generations of software developers and users will enjoy the four freedoms, as follows:
– The freedom to run the program as you wish, for any purpose (freedom 0).
– The freedom to study how the program works, and change it so it does your computing as you wish (freedom 1).
– Access to the source code is a precondition for this.The freedom to redistribute copies so you can help your neighbor (freedom 2).
– The freedom to distribute copies of your modified versions to others (freedom 3). By doing this you can give the whole community a chance to benefit from your changes. Access to the source code is a precondition for this.
Discussion on the four freedoms will be a long discussion and is best explained on the FSF website. Why are we counting from 0 to 3? It is something you should ask me if we meet. It is a good start of a conversation. Any computer science or computer engineering student or graduate should know, by the way.
One thing I noticed was that Stallman was barefoot while speaking to the audience. During the question and answer, he requested the ones asking questions to speak loudly and clearly as he has difficulty hearing. He also wanted the questions to be direct to the point.
As the session was drawing to an end and the participants where preparing for the group picture, I saw Stallman trying to put back his shoes on. I noticed that it seemed difficult for him to do that so I asked, “Richard, do you need help?”. And he said, yes and mumbled something about pain on his shoulders if he stretched his arms towards his feet.
And so there I was, at the right place and right time, to help Richard Stallman put back his shoes on. I’m sure this is a non-significant event in the overall chain of events in the IT world. But I can say to myself, I have paid back a little bit to the founder of FSF. If not for his work, the Internet might be a different thing and I may be somewhere else.

Richard Stallman putting back his shoes on with a little help from Jerome Auza.

Richard Stallman (3rd from the left, bottom row) poses with the participants.
by admin | Mar 28, 2015 | Headlines, Tech Talk
Richard Stallman, founder of the Free Software Foundation (FSF), spoke to students and IT enthusiasts at the University of the Philippines – Cebu City on March 28, 2015 about copyright issues on software.
Stallman is the original author of GCC, the most popular compiler for the C programming language. GCC is the used to compile software that runs email servers, web servers, routers and many other systems on the Internet.
Aside from his technical contributions, Stallman is also known for his advocacy “to promote computer user freedom and to defend the rights of all free software users”. The FSF provides critical infrastructure and funding for the GNU project, the foundation of the popular GNU/Linux family of free operating systems and the keystone of the Internet.

Richard Stallman, Founder of the Free Software Foundation, speaks to students and IT enthusiasts at UP Cebu.
In his talk, Stallman raised issue on the creeping loss of freedom to use software and other digital and non-digital works like art and literature. He also talked about the history of copyright and its original purpose which is for the good of the general public.
At present, influential companies try to change the original purpose of copyright and subvert it to benefit the companies instead of the general public. One such example he gave as music. In the past, it was easy to share music: you just lend your CD to your friend. Now, with streaming music service, you cannot just lend the service to you friend because the service provider restricts it.
Stallman warns that if nothing is done, we will eventually lose all our freedom to use software the way we want to use it.
by admin | Mar 28, 2015 | Tech Talk
By: Jerome Auza
The latest ranking of ICT councils placed Bohol last among 42 other cities and provinces even with the efforts of the provincial government and the Bohol ICT council in the past years to influence the improvements in telco services, power situation and general readiness for ICT enabled services.
The BICTC’s new set of officers, who were elected in March 4, 2015 during the general assembly held at the Panda Tea Suites conference room, accepted this news as a challenge going forward. The council has already recognized the challenges in Bohol as the province tries to be a destination of choice for BPOs.
While Bohol is already connected via fiber optic cable to the domestic fiber optic networks of both Globe and PLDT, the so called last mile services, still needs a lot of improvement. Internet access service, in general, is not as reliable as users expect, even for business accounts. But Internet connection is not our only challenge.
We have an issue on the reliability of our power supply. We are very dependent on the single link to the national grid in Leyte. This was painfully clear in November 2013 after typhoon Yolanda severely damaged the power infrastructure in Leyte and Bohol was plunged into extended blackouts. Until we have a second link to the national grid, perhaps going to Cebu, we have a single point of failure for our power supply. Or perhaps, Bohol should have its own power production capability, preferably from renewable sources.
On the other hand, there is a thriving small and medium IT enterprises or SMITES in the province, making do with the available telco services. You may have not known yet that a small group of Boholanos are developing very advanced analytics software used around the world already. We have a group of mobile apps developers who are experimenting on various apps . Also, there is an unrecorded number of free lancers that make a living doing various services like software development, graphics editing, drafting and content production.
Aside from these SMITES, Bohol also has several entrepreneurs that developed innovative products and services that are uniquely Boholano but not directly ICT-enabled. Maybe Bohol should also promote the stories behind the products and services of these entrepreneurs. The province should position itself as a place of innovation, no matter what the field.
Then we use ICT-enabled services and systems to promote our own entrepreneurs. Maybe it’s the way to go in exploiting ICT to increase jobs in Bohol rather than try to invite BPO locators that have stringent prerequisites that would still take years for Bohol to put in place.
by admin | Mar 21, 2015 | Tech Talk
Structure Cabling System Series
By: Jerome Auza
A company setting up a wired network should carefully choose the type and quality of the network cables used. Unfortunately, there are a lot of fake network cables sold in computer supply shops and hardware stores. One should be careful when purchasing network cables.
There are several types of cables that may be used. For small networks, usually the unshielded twisted pair or UTP of the type Cat5e is used. Cat5e is a name of the standards defining the performance characteristics of the cable which is capable of 1000mbps speed. For larger networks or for high speed requirements up to 10gbps, the Cat6 standard is used. In environments where electrical or electromagnetic interference is unavoidable, the shielded twisted pair (STP) is used.
When buying network cables, make sure to purchase them from suppliers that sell only original products. There are many fake network cables sold and possibly the owners of the stores are not aware that these are fake products.
Inspect the copper wires within the plastic cover of the cable. These wires should feel thick and firm not not flimsy. The fake cables use thinner and lower grade materials that are easy to tear apart. You can tell if the wires are too thin if the wires inside doesn’t seem to fit snugly inside the plastic cover.
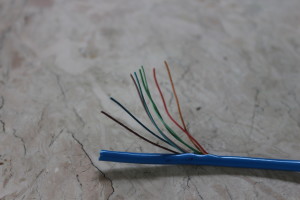
I took pictures of fake or incorrect cables that may be sold in local stores in Bohol and compare them with an original cable. Figure 1 is an original cable. There should be 4 twisted pairs inside the Cat5e cable with the following colors: brown, blue, green and orange. Each twisted pair consists of a wire with full color insulation and another wire with insulation that is white and lined with the same color. The wires are firm and should not be flimsy. The cover should not easily tear apart. Most Cat5e cables would also contain a very thin but strong string that when pulled down to tear the cover.

Figure 1. An original cable with 4 twisted pairs. The wires are firm and a thin string is included in the wire and can be used to break open the cover as it is very hard to tear without tools.
Figure 2 is an obviously fake cable. The four pairs of wires are not twisted, are thin and flimsy and some wires are of the wrong colors. The cover could be torn apart easily using fingernails.
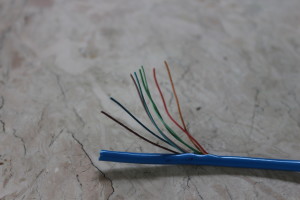
Figure 2. Fake cable sold as Cat5e. The wires are not twisted pairs and also are easy to break. The cover of the cable is easy to tear apart.
Figure 3 seems to be of the right type of wire but there are only two pairs. While this wire can work because only two pairs are required for a 100mbps network, this cable will not work for applications requiring power over ethernet or POE. Also, it will not work for gigabit networks because 1000mbps requires the four pairs to work reliably.

Figure 3. This cable looks correct with the wires twisted in pairs. However, there should be 4 twisted pairs or 8 wires within the cable.
by admin | Mar 14, 2015 | Tech Talk
Structure Cabling System Series
By: Jerome Auza
In the next several weeks, I will discuss about structured cabling practices and components for computer networks. I am frequently asked about computer networks and what’s the best approach to implementing a reliable and flexible computer network.
One of the questions I’m often asked is “Is it still necessary to use a wired network for my company with WiFi technology available?” My answer is yes, especially if there are many users and you need to share a printer on the network. As the number of users connected to an access point increase, the efficiency of the wireless network connection decrease. Also WiFi is very susceptible to interference and unencrypted connections are vulnerable to eavesdropping.
There are two major components in a computer network: the passive component and the active component. The passive component of the network include the cables, patch panels, jacks, patch cords, cable managers, cabinets and all other materials used in the physical installation of the network. The active components are the switches, routers and other network devices.
I have seen a lot of “spaghetti” network implementations where the wires just go anywhere and over time, the computer network looks a lot like spaghetti. This is usually because a company may start with just one computer and then as they grow bigger, more computers and devices are added but the network doesn’t get upgraded.
In implementing a computer network, part of the physical network should stay fixed on the building structure. To connect to the network, the user will need a patch cord to connect the computer to the data outlet jack. The patch cord is the movable part of the network and gives you the flexibility of changing the position of the computer at a later time without modifying the fixed part of the network.
The correct setup would be as follows:
1. The computer is connected to the data outlet jack via a patch cord
2. The opposite end of the data outlet jack is the patch panel. In other words, the network cable connects the jack to the patch panel
3. From the patch panel, another patch cord connects the port on the patch panel to the router or switch.
The data outlet up to the patch panel is the fixed part of the network. When done properly, the fixed part of the network should be reliable over many years. The patch cords allow the network administrator to be flexible in connecting various devices which could change over time. The result is a flexible and reliable network that could last for many years.
Aside from proper cabling practices, the quality of the components used is very important also. Unfortunately, there are many network cables, patch cords and other components that are not really of standard quality. Sometimes, even fake materials can be sold in stores so it is important to purchase materials from an authorized supplier.
For small networks, the Cat5e standard for network materials is usually sufficient and would be the most cost effective. For applications needing gigabit speeds, Cat6 network materials would be appropriate but it can be more than double the cost of Cat5e materials.
Next week, we shall look in detail at the network cable and patch cords and discuss the important points in purchasing and installing these cables.

Patch cord connected to the computer (2nd cable from the front)

Patch cords connected at the patch panels.

Patch cord connected to a data outlet jack.